Access to a website or a more modern equivalent of a service, application or platform provided over the internet may be blocked. So what is access blocking, how does it happen?
Ben Av. Alp Öztekin, I will now be on Webtekno with my articles on internet and informatics law. My purpose for the articles I will present to the reader here is not to bombard the reader with legal information. On the contrary, keeping the required theoretical legal knowledge to a minimum, “Internet and Law” I intend to share articles on the title of which the technical, sociological and philosophical aspects outweigh.
Firstly, blocking access to the internet I decided to present the subject to the reader. In order to explain the subject, I first explained the information about the origin and functioning of the internet, then the activities of the access providers on this structure and the practices regarding the blocking of access.
What is the Internet access barrier and how is it done?’ The subject was explained under the following headings:
- Internet and Internet Access Concepts
- Access Providers and Their Domination over the Backbone
- The Concept of Denial of Access
- Blocking Access Legally or by Hacking
- ?Which Methods Are Used to Legally Block Access?
- General Methods
- Methods Related to Server IP Addresses
- URL-Based Blocking Methods That Can Also Provide Network Control
A) Internet and Internet Access Concepts
First of all, I would like to explain how the internet works and how internet users access the network so that the reader can understand what blocking of access means and how it can be achieved.
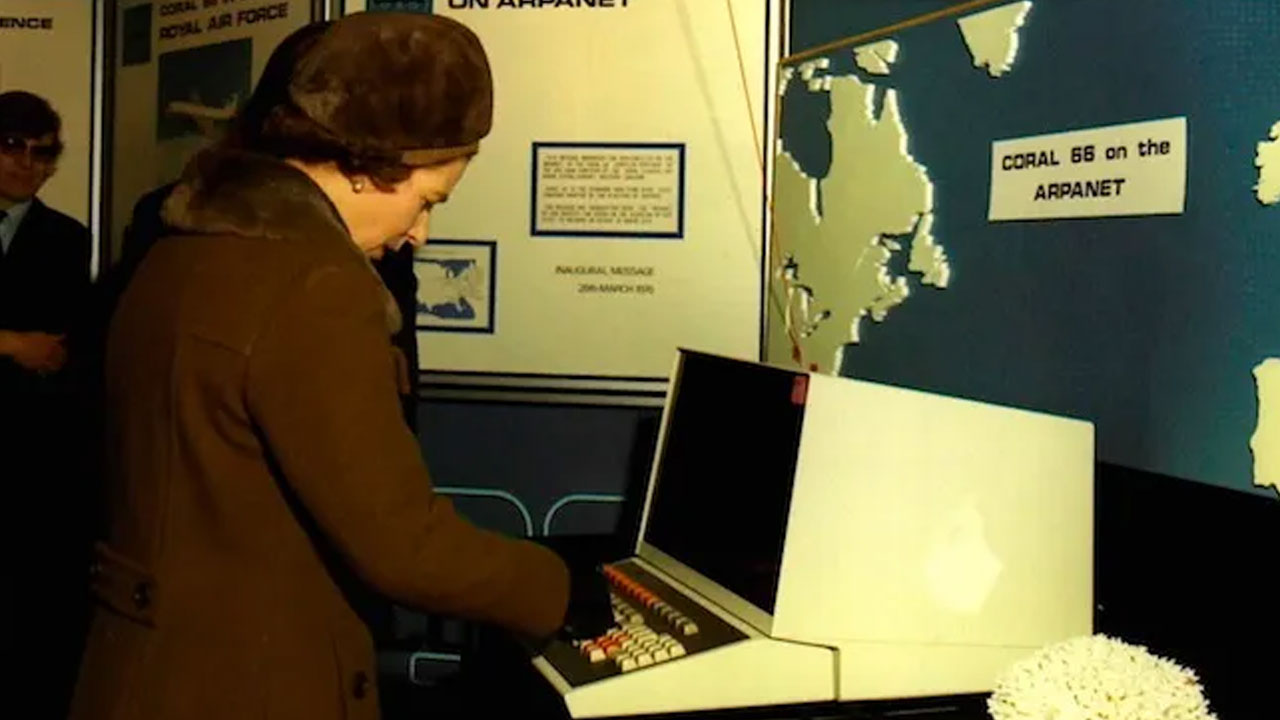
The foundations of the Internet were laid over six decades ago by the US Department of Defense’s (DOD) ARPA unit. ARPANET It started as a project. A network structure was developed in ARPANET that shares data between remote devices. Alternative network structures followed the combination of local networks over ARPANET, and these became interconnected within the country over time.
This structure, in which many LANs combined and WANs connected to each other, later crossed the borders of the USA, and many networks in different countries were connected to each other with terrestrial and submarine cables. In addition to FTP platforms, browser software has been developed to access databases on LANs, Gopher and WWW-http born. (Later Gopher died…) Here we call this global structure where information devices can communicate with each other, the Internet.
Accessing this internet network, which expresses the combination of many intertwined LANs and WANs, connects the user from his own local network to global WANs, and finally to a server in another network, using the internet backbone formed by cables, base stations, satellites connecting the networks in the world. and it means communication. like this An internet user in Istanbul, over its local network; It can reach the backbone in Turkey, passing IXP points over this backbone, to any point on the other end of the backbone, for example a server in the USA.
B) Access Providers and Their Domination over the Backbone

As explained above, the internet backbone is a global network structure that connects devices to each other, and the birthplace of this network is the USA. Various companies have built and operate this internet backbone. These companies are called access providers. Global access provider ISPs generally connect the world with cables passing over seas and land. Since internet traffic in the world passes through this multi-owner network structure, cooperation between these ISPs and certain points in various parts of the world are also possible. internet exchange points (IXP) has. There are also national access providers that have their own local backbone, and while domestic traffic flows through these companies’ backbones, outbound traffic usually flows through global ISPs.
The access provider ISPs described above are the actual operators of the backbone. However, they also lease the backbone they operate to third-party access providers, so that many ISPs can provide services even though there is only one ownership on the same backbone. By subscribing to all these ISPs, internet users log out to the internet network over their local networks.
C) The Concept of Denial of Access

In the simplest sense, blocking access means that the client and server cannot communicate over the internet backbone. Internet user’s access to the Internet from his own local network can be blocked completely, as well as access to servers at certain points of the Internet and even only to certain data within the servers. For example, an internet user can be completely blocked from accessing Youtube. Access to a single video on Youtube or even a single comment within the video can be blocked.
C.1) Blocking Access Legally or by Hacking

(The legal aspect of the matter will not be detailed here.) In general, there are various regulations in Turkish law to prevent access in many legislations. Apart from these, 5651 p. In the Law, how access can be prevented has been specified and has been reduced accordingly. Here are the legal infrastructure, IP / DNS / URL-based blocking and similar methods and duly applied barriers ‘legal barriers’ is called. These technical methods, which will be explained in detail below, are user, that is, internet subscriber based and backbone blocking.
However, the user side or backbone does not need to be involved to block access to an internet content. If a hacker wants It can also block access with DDoS attacks. Again, by creating fake DNS or proxy servers and even setting up a fake router (these methods are called man in the middle), it can reach clients to different points of the internet or disrupt access. All these consequences are undoubtedly to prevent access by hacking. Obviously, these methods are illegal and will constitute a crime.
So, the main point to be understood here is that legally blocking access can only be done through the ISPs operating the backbone and with the knowledge of them, in accordance with the law.
D) Which Methods Are Used to Legally Block Access?
D.1. Generally
Let’s consider a large corporate network topology with hundreds of devices connected. Numerous The VLAN is nested, A huge structure to which switches and routers are connected… The network administrator can control this network, examine the data packets in depth using analysis software or beyond using DPI, and thus, if he uses the necessary technology, he can read the communication in the content of each data packet in the network, including the correspondence in the mobile applications.
The network structure in a country is also similar to the example above. The only difference is that if more than one ISP operates in the country, the number of administrators will be more than one, and these administrators will technological infrastructure used may also differ.
D.2. Methods Related to Server IP Addresses (Blocking Access to the Whole Site)
In Internet communication, client and server IPs are the main point in communication, since protocol sets in the DOD standard model and generally TCP/IP-UDP operate. (The people who control the LAN can well only ensure that devices with allowed internal IP and MAC addresses can only access certain points on the internet, which in practice can be considered denial. But that’s not the point.)
The main point in the access blocking techniques performed by the access providers specific to the IP address are the routers and DNS servers that take the client to the internet. The router/modem, which takes the Internet user to the backbone of the ISP to which he is subscribed, can be adjusted so that the user does not access servers with certain IPs and ports. This is the most typical technique of access barriers. In this way, its IP addresses and ports are known. access to the servers of any site can be blocked Access to DNS servers such as VPN servers or TOR servers can also be blocked.
The second method in IP-specific blocking is not the web servers on the other side of the communication, but the use of DNS servers that map domain names to IP, including domain names. In order for this system to be successful, the internet subscriber’s device must not be connected to alternative DNS servers, DNS server controlled by the access provider must be set to send requests.
Since these traditional methods target server IP and ports, they prevent access to the entire site or application. Even mail etc. on the same server. In the use of the systems, if the server is divided, these services over different IP/ports if not submitted, mail etc. Access to services may also be blocked.
D.3. URL-Based Blocking Methods That Can Also Provide Network Control
When a site is completely blocked, if the social importance of this site is high and the number of users is huge, a problem based on the “right to access the Internet” arises. Although thousands of websites are completely blocked and nobody cares Sites with a large number of users, such as Youtube and Wikipedia When access is completely blocked, various legal and ethical problems arise, as all internet users are prevented from accessing areas of the sites that are not related to unlawfulness.
The power to ensure that these problems do not arise is technology at its core. As will be remembered from the example of the corporate network above, the more technology in the hands of the network administrator, the more his dominance of the network will increase. So the point to remember is this: high-level network technologies first create a serious dominance in the network, and then create possibilities such as URL-based blocking. Thanks to this serious dominance, data packets its content is fully watchable and readable may become.
In order to provide a URL-based blocking, it is necessary to control the traffic on the network and to be able to interfere with the data traffic on the network. The result reached at this point; Besides the existence of a wide variety of hybrid technologies, there are two methods that are particularly used. These are ISPs passing traffic through proxy and/or setting up packet analysis systems. Thanks to these technologies, most layers of data packets become accessible and controllable. In this way, access to a single video or article on the website can be blocked by implementing URL-based access barriers. As the technology develops, your area for URL-based blocking increases and, for example, in structures such as SSL that provides encrypted communication, and even Dominating data flowing over VPNYou can provide t. In packet analysis systems, this can be achieved by using technologies related to DPI, that is, deep packet analysis systems.
(We do not know how each access provider imposes an access block in Turkey. There is no binding rule on this subject anyway. According to the Law, p. 5651, access providers are expected to block access to sites or URLs using certain similar methods, which is true. This is.)
Recommendation to the Reader:
If readers want to understand more deeply the structure of the blocking of access; To understand the development of this structure, URL-based blocking processes and the formation of SORM, a serious DPI technology, in Russia Relevant parts of the book THE RED WEB by Andrei Soldatov and Irina Borogan they can read.
Hunting. Alp Öztekin – Email for questions and comments: [email protected]
