Roughly speaking, how exactly do the password managers to whom we entrust our login information, address and bank card information on 50 sites protect our information?
We used it in the era when computers started to enter every home. with 123456789 And with QWERTY The reason why we abandon our passwords and switch to new passwords that are quite complicated compared to them is cyber security They had concerns. More and more every day website and app Since it is available, the number of passwords we need to remember is increasing.
That’s why most of us either use the same/similar password everywhere or have to keep a lot of different passwords in our minds. However, when some applications ask us to change the password periodically, everything can go upside down. For this reason and because the number of passwords is increasing, many people password manager He is undecided whether to use it or not.
The most basic question: What is this password manager?
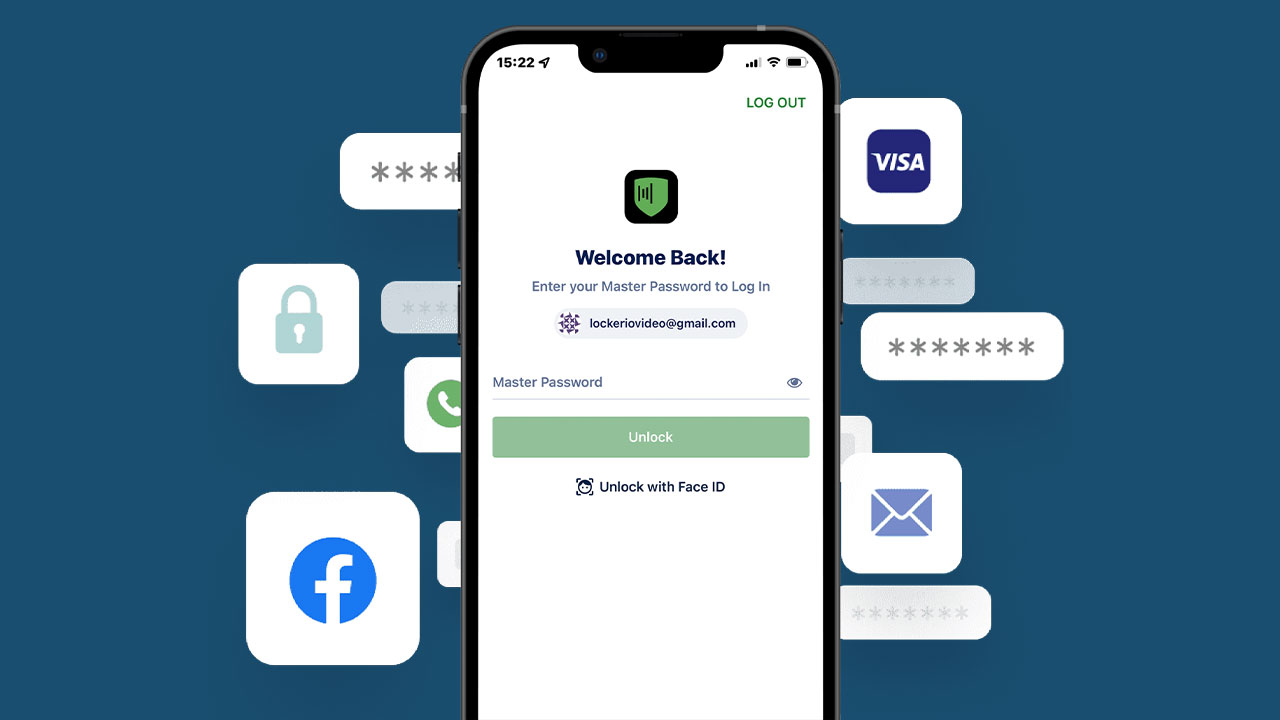
Password managers; They are digital safes that allow you to store information such as address, phone number and bank card in addition to your passwords. This safe, which contains your passwords, stores your password and address information when you want to log in somewhere. automatically It makes filling in easier.
When you want to make a purchase, use your wallet. take out your card You can transfer your card information without having to enter the numbers. Although all this sounds good, we need to enter one of these applications where we enter our data. cyber attackers Imagine reaching it. Can’t these people, who only have access to one application, easily obtain all our passwords?
Let’s explain why this is extremely difficult, without getting confused.
Avoid these password managers because they are so common. LastPass Let’s take it as a basis. When you want to store your passwords here, you first create a LastPass account and create a password for this account. master password You determine. Of course, this is different from the password you use for Webtekno membership, for example.
When you create your account plugin or app As a password manager, it asks for permission to save your user information on the sites you visit. In this way, your information is placed in your private safe. Then Google automatic form filling LastPass can take over the feature.
Since LastPass itself is a cloud-based service, your LastPass vault containing your passwords On LastPass servers hiding. So how is security here ensured?
When you want to access your password safe, you first create a key to open this safe. To do this, you first enter your master password. After the verification step, your master password and e-mail address will be sent to you with the latest updates. out of 600,000 combinations passing by one safe key It creates.
After this, all that remains is to access our vault on the server. For this, the password formed by combining our e-mail address and password 600,000 times is again entered into 600,000 combinations with our master password and transmitted to the safe on the server. without seeing our master password He realizes that we are the ones trying to access the safe.
As a result, we obtain one verification and one safe key. verification key to the vault on the server While it provides us with access, the safe key also enables us to open it. To ensure the security of both keys, your master password must be strong.
In other words, while a key you create opens a key leading to the safe, the other key you create in addition to it helps you open that safe.
And you need to enter the password needed to create this key in the first place. LastPass You do not forward it to password managers such as. Therefore, even if a copy of your safe is compromised, as we will discuss shortly, it is almost impossible to open it. “AlmostThe ” part is important at this point.
“So can we trust them right now?” Although the question will come down to a personal decision, let’s touch on the unfortunate events that LastPass has experienced recently.
LastPass at different times last year exposed to cyber attacks. As a result, information such as the names of the websites where the passwords were registered, billing addresses, phone numbers and IP addresses fell into the hands of the attackers. In addition, users’ safe backups were also seized. These include both unencrypted website addresses and username and passwords It contained encrypted information such as.
But we said that LastPass does not know our master password and that safes can only be opened this way. The company also included this in its statement. However, the attackers still use these safes. with brute force and phishing methods Stating that they can try to open it, the company recommended that people, especially those with a weak master password, change their saved passwords.

Last January, the parent company of LastPass GoTounder the umbrella of the company from the attacks in question Other services are also affected explained. However, this time, it was announced that some user names, encrypted passwords and 2-step verification settings were also leaked, although not completely. Although this does not mean that the accounts have been completely leaked in itself, it does mean that the phone numbers, addresses and emails are in the hands of the attackers.
This means that they will be able to reach people whose information has been seized more easily.
Regarding this issue, which still has an impact, we last learned that the crypto wallets of different people were emptied.
Affected by LastPass data leak, data based on October 25 25 people cryptocurrency wallet was infiltrated and in total $4.4 million worth of robbery was committed. According to Metamask and ZachXBT, a total of 80 cryptocurrency wallets were affected by the attack. As a result, more or less $35 million money was stolen.
But how did the company that provides so much security for us come under such an attack?
In the first attack on August 12, software engineer Inconsistent movements were observed on an employee’s device. Developer resources When it was realized that the accessing computer was compromised, access to the resources was cut off. The attacker, who accessed the development environment by hiding his location with a VPN, obtained the domain information and two-step verification of that employee to do this. In this attack, only source codes were seized.
The second attack, in which data backups were taken from the cloud environment, was a continuation of the first. The attacker, who wants to access the information he has obtained, requires one of the 4 developers who have the necessary key to do so. He installed a keylogger on his personal computer at home.. In this way, when the developer entered the password, the attacker also learned the password. In this way, the leak situation that we are still seeing the effects of broke out.
Now should we trust them or not?
How these -cloud-based- applications work LastPass We explained it to you through an example. Even if such an incident had not happened, we would recommend that you do not entrust your most valuable passwords to different places, and we can still say that this is more logical. As soon as the vulnerabilities in question emerge, developers close that gap. But that doesn’t change the fact that password managers are still fundamentally more secure.
As a result, even if your account has been accessed, the combination of the password you specified must be known in order to see the passwords. Therefore, our duty is to leave the final decision to you after providing information on this issue.
RELATED NEWS
Why is contactless payment considered safer than inserting a card and entering a password?
RELATED NEWS
